Introduction
HIPAA carries real enforcement weight - penalties for willful neglect violations reach up to $2.19 million annually - yet its technology-neutral language leaves critical implementation questions unanswered. NIST fills that gap with the technical operational structure that translates HIPAA's broad mandates into actionable controls, but it's voluntary, not legally binding.
IT teams in healthcare and regulated industries carry both frameworks simultaneously. That dual burden is more nuanced than most compliance guides acknowledge.
Healthcare organizations, business associates, and regulated enterprises are expected to operate under both frameworks simultaneously, yet most IT guides treat them as separate compliance exercises. This creates gaps: teams either focus on checking HIPAA's legal boxes without operational rigor, or build robust NIST-aligned security programs that don't map cleanly to regulatory requirements.
This guide explains what each framework requires, how they officially map to each other via the OCR crosswalk, how to implement alignment in practice, and why AI deployments introduce a new layer of compliance complexity that neither framework originally anticipated.
TLDR
- HIPAA is legally mandatory for covered entities and business associates handling ePHI, with flexible but enforceable safeguard requirements
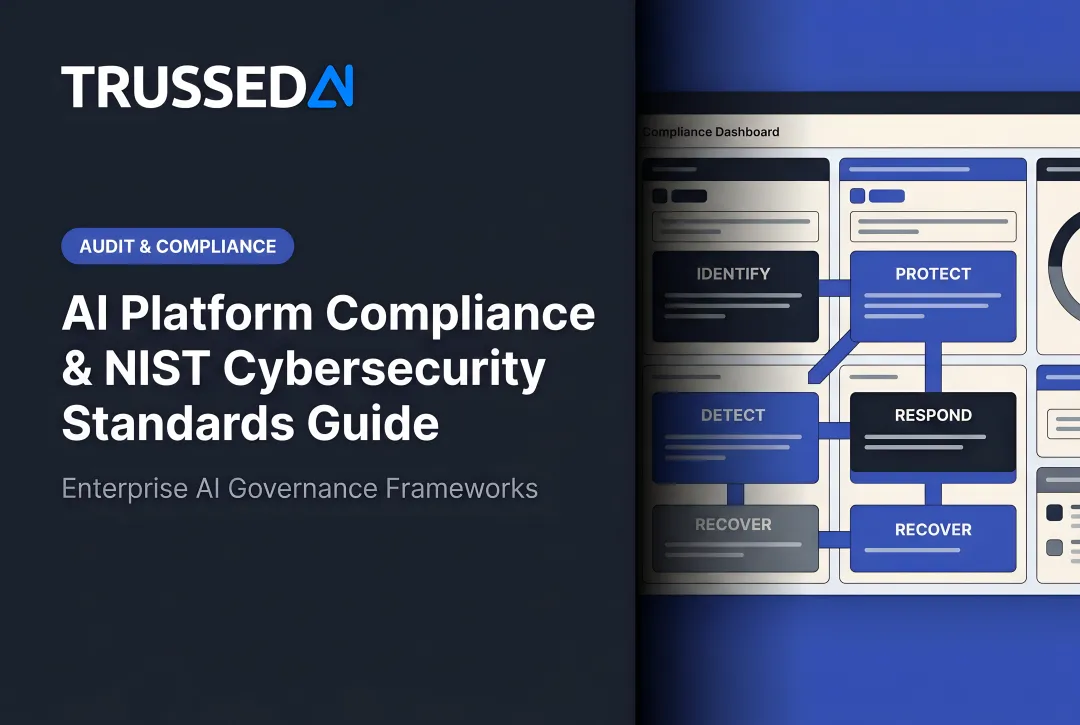
- NIST CSF supplies the technical "how" behind HIPAA's "what," built around six functions: Govern, Identify, Protect, Detect, Respond, and Recover
- HHS OCR published an official crosswalk mapping HIPAA Security Rule requirements directly to NIST CSF controls
- Used together: HIPAA keeps you legally compliant, NIST keeps you operationally resilient
- AI systems handling ePHI require runtime policy enforcement that static compliance documentation cannot provide
HIPAA Security Rule: Core Requirements for IT Compliance
HIPAA applies to covered entities,healthcare providers, health plans, and healthcare clearinghouses,and their business associates, including MSPs, cloud vendors, billing firms, and AI tool providers that process ePHI on their behalf. Business Associate Agreements (BAAs) extend HIPAA obligations contractually down the supply chain, making third-party risk management a critical compliance component.
Administrative Safeguards
Administrative safeguards address governance and process. Organizations must appoint a designated security officer, conduct regular risk analyses, establish workforce security training, and create documented incident response procedures. These are the most commonly cited deficiencies in OCR enforcement actions.
Failure to conduct an accurate and thorough risk analysis remains the #1 enforcement target. Recent settlements illustrate the financial consequences:
- Warby Parker paid $1.5 million in 2025 for failing to conduct a HIPAA-compliant risk analysis and monitor information systems.
- MMG Fusion settled for $10,000 (reduced due to financial condition) after a breach affecting 15 million individuals,cited primarily for risk analysis failures.
Physical Safeguards
Physical safeguards cover facility access controls, workstation use policies, and device/media controls. In hybrid cloud environments, "physical" requirements extend to data center agreements with cloud providers. Physical access controls apply wherever ePHI resides,on-premises or in a vendor's facility.
Technical Safeguards
Technical safeguards include four categories:
- Access controls: Unique user IDs, automatic logoff, and emergency access procedures
- Audit controls: Hardware and software logs tracking ePHI access
- Integrity controls: Ensuring data isn't improperly altered or destroyed
- Transmission security: Encrypting ePHI in transit
Encryption is "addressable" but considered a de facto requirement by OCR in most contexts. "Addressable" doesn't mean optional: entities must implement it if reasonable and appropriate, or implement an equivalent alternative and document the justification.
HIPAA Penalty Structure
These technical and administrative requirements carry real financial consequences when violated. The 2026 inflation-adjusted penalty tiers raise the ceiling on per-violation fines:
| Tier | Description | Min Per Violation | Max Per Violation | Annual Cap |
|---|---|---|---|---|
| 1 | No Knowledge | $145 | $73,011 | $36,506 |
| 2 | Reasonable Cause | $1,461 | $73,011 | $146,053 |
| 3 | Willful Neglect (Corrected) | $14,602 | $73,011 | $365,052 |
| 4 | Willful Neglect (Not Corrected) | $73,011 | $2,190,294 | $2,190,294 |
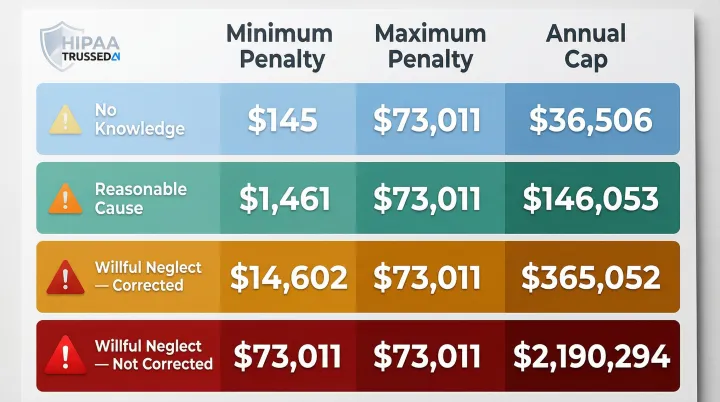
Avoiding a Tier 4 classification starts with documentation. All required records,policies, procedures, risk assessments,must be retained for six years under §164.316(b)(2). Without that paper trail, "willful neglect" becomes the default finding.
NIST Cybersecurity Framework: Structure and Key Functions
The National Institute of Standards and Technology designed NIST CSF as a voluntary, risk-based framework that any organization can adapt regardless of size or sector. Its technology-neutral structure maps cleanly to HIPAA's outcome-based requirements, making it a practical operational companion to the law.
The Six Core Functions
NIST CSF 2.0, released February 2024, expanded the original five functions by adding Govern:
| Function | Focus Area | HIPAA Relevance |
|---|---|---|
| Govern | Cybersecurity governance, leadership accountability, supply chain risk | Formalizes executive ownership of security posture; covers third-party vendor oversight |
| Identify | Asset inventory, risk assessment, data classification | Know what ePHI you hold, where it lives, and who can reach it |
| Protect | Access management, training, encryption, configuration management | Controls that prevent unauthorized access and data breaches |
| Detect | Continuous monitoring, anomaly detection, audit log review | Catch security events before they escalate into reportable breaches |
| Respond | Incident response planning, containment, notifications | Documented procedures minimize damage and keep regulatory timelines on track |
| Recover | Business continuity, disaster recovery testing | Demonstrate ability to restore ePHI availability and integrity after disruptions |
NIST CSF vs. HIPAA: Structural Differences
HIPAA is a law with enforcement, audits, and penalties. NIST CSF is a voluntary framework. However, OCR has explicitly encouraged HIPAA covered entities to use NIST CSF, and documented NIST alignment can serve as evidence of good-faith effort during breach investigations. In practice, OCR investigators look for evidence that an organization ran a documented risk analysis and acted on its findings , exactly what NIST CSF's Identify and Govern functions produce.
How HIPAA and NIST Align: The OCR Crosswalk Explained
The OCR crosswalk was jointly developed by HHS Office for Civil Rights, NIST, and the Office of the National Coordinator for Health IT. It provides control-by-control mapping between NIST CSF subcategories and HIPAA Security Rule standards and implementation specifications.
Using the crosswalk does not guarantee HIPAA compliance,OCR explicitly warns that aligning with NIST CSF "does not imply or guarantee compliance with any laws or regulations." However, it provides a structured roadmap for identifying gaps and demonstrating systematic risk management.
Key Mapping Examples
§164.312(b) → DE.AE-3 (Audit Controls): NIST's anomaly and event detection subcategory maps to HIPAA's technical safeguard for audit controls, which requires hardware, software, and procedural mechanisms to record and examine ePHI access. HIPAA mandates audit controls; NIST specifies what they look like: aggregating and correlating event data from multiple sources and sensors.
§164.308(a)(7) → RC.RP-1 (Contingency Planning): NIST's recovery planning subcategory maps to HIPAA's contingency plan standard under administrative safeguards, which requires data backup, disaster recovery, and emergency mode operation plans. Organizations following NIST recovery guidance can directly map their controls to these HIPAA requirements during audits.
Using the Crosswalk Operationally
Four steps make this crosswalk actionable:
- Identify the HIPAA Security Rule standards your organization must meet
- Locate the corresponding NIST CSF subcategories in the crosswalk
- Assess your current control maturity for each subcategory
- Document gaps , this record becomes your remediation plan and the evidence OCR investigators look for when evaluating whether your risk management was systematic
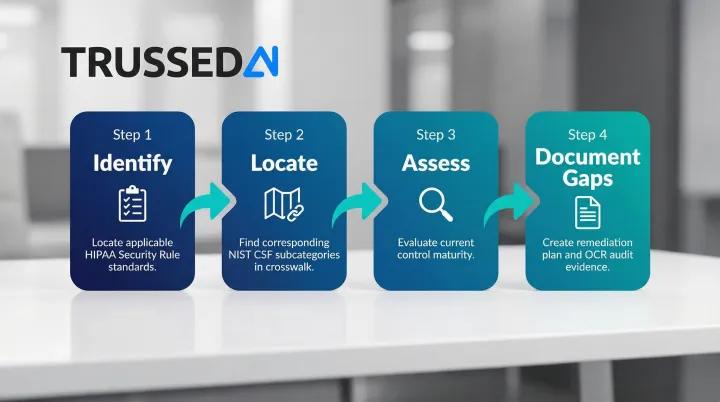
Organizations that follow this process don't just prepare for audits , they build a continuous compliance posture that holds up under scrutiny.
Implementing HIPAA-NIST Alignment: A Practical IT Roadmap
Step 1: Conduct a Comprehensive Risk Analysis
HIPAA requires a formal risk analysis (§164.308(a)(1)) as the foundation of the entire Security Rule , and it's the most frequently cited deficiency in OCR settlements. Use NIST SP 800-30 to structure this process before mapping any controls.
Key inputs for the analysis:
- All ePHI locations and data flows across systems
- Threat sources, threat events, and existing vulnerabilities
- Likelihood and impact ratings for each identified risk
OCR expects continuous, ongoing assessment rather than point-in-time checklists. Trigger a formal review whenever new technologies , including AI systems , are planned or deployed.
Step 2: Run the Crosswalk Gap Analysis
Map current controls against NIST CSF subcategories using the OCR crosswalk document. As you work through it:
- Categorize gaps by HIPAA safeguard type: administrative, physical, and technical
- Prioritize remediation based on likelihood and impact of exploitation
- Document all findings , this record satisfies HIPAA's requirement for written security policies and procedures
Step 3: Establish Continuous Monitoring and Evidence Generation
HIPAA compliance is not a point-in-time certification. OCR expects ongoing monitoring, at least annual risk assessments, and documented reviews whenever operational changes occur. NIST CSF's Detect and Respond functions provide the operational model for this.
In practice, that means:
- Automated log collection and access anomaly detection
- Periodic control testing with documented results
- Audit-ready evidence retained for at least six years per HIPAA's documentation retention requirements
AI Systems, HIPAA, and NIST: The Emerging Compliance Challenge
AI systems create a new risk surface in HIPAA-governed environments. AI applications, conversational agents, and automated workflows access, process, or generate outputs containing ePHI,often across multiple models, APIs, and third-party Solution. A late 2024 McKinsey survey found that 85% of healthcare leaders were exploring or had adopted generative AI capabilities; a 2024 HIMSS and Medscape report put active AI adoption at 86%.
That rapid uptake introduces third-party vendor risk at a scale traditional controls weren't built for,a concern the 2024 Verizon Data Breach Investigations Report underscored by expanding its breach taxonomy to include third-party partner infrastructure.
Unlike traditional software with static data flows, AI systems are dynamic: the same prompt can produce different outputs, agents can access data in unplanned sequences, and the boundaries of "who accessed what and when" become blurry. Traditional audit mechanisms were built for structured data systems. AI agents don't leave standard access logs.
The Runtime Governance Gap
HIPAA requires audit controls and access logging, but traditional mechanisms can't capture how AI agents interact with ePHI. NIST CSF 2.0's Govern function calls for formal AI governance policies,yet most organizations haven't operationalized these into runtime enforcement. The gap between having a policy and enforcing it at the moment an AI model touches ePHI is where violations occur.
Under 45 CFR 160.103, any vendor that creates, receives, maintains, or transmits ePHI on behalf of a covered entity is a business associate requiring a BAA. This applies directly to AI vendors. Common examples that trigger the BAA requirement include:
- AI chat tools where clinicians input patient details
- Ambient listening scribes that capture and transcribe patient encounters
- Predictive models that process diagnosis or treatment data
- Third-party APIs that route ePHI between systems
OCR guidance on online tracking technologies confirms that vendors receiving ePHI require BAAs when they meet this definition,regardless of whether the tool is marketed as "AI" or not.
Operationalizing AI Governance
Runtime governance means enforcing policies at the point of AI interaction,not after the fact. Platforms like Trussed AI's enterprise AI control plane address this gap by enforcing policies at the execution layer, automatically generating audit trails as a byproduct of every governed AI transaction. This provides the continuous compliance monitoring and documentation that both HIPAA's audit control requirements and NIST CSF's Detect and Govern functions call for.
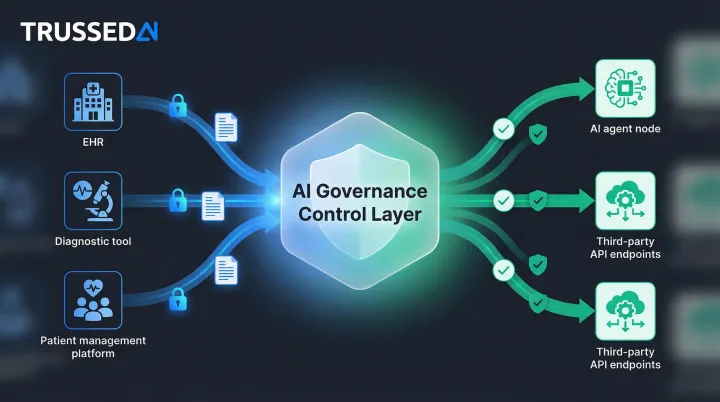
For healthcare organizations deploying AI tools that interact with patient data, this means compliance evidence isn't assembled after a review,it's generated automatically at every governed interaction, making audit readiness a default state rather than a periodic scramble.
Frequently Asked Questions
What is the NIST Cybersecurity Framework for HIPAA?
NIST CSF is a voluntary cybersecurity framework that HHS Office for Civil Rights officially recommends as a tool to help HIPAA covered entities implement the Security Rule. While not legally required, it provides specific technical controls - covering areas like access management, incident response, and encryption - that HIPAA's technology-neutral language intentionally leaves undefined.
What are the five core functions of the NIST Cybersecurity Framework?
The five original functions are Identify, Protect, Detect, Respond, and Recover. NIST CSF 2.0 (released February 2024) added a sixth function - Govern - which addresses organizational policy and leadership accountability for cybersecurity.
Is NIST compliance required for HIPAA?
No , but OCR actively encourages covered entities to adopt it and has published an official crosswalk mapping NIST CSF to the HIPAA Security Rule. Documenting NIST-aligned controls strengthens your position during audits by demonstrating good-faith compliance efforts.
What is the OCR crosswalk between HIPAA and NIST?
The OCR crosswalk is a document jointly published by HHS, NIST, and ONC that maps each HIPAA Security Rule standard to corresponding NIST CSF subcategories. It helps organizations identify security gaps and demonstrate how their NIST-based controls satisfy HIPAA requirements.
What are the three safeguard categories under the HIPAA Security Rule?
The three categories are administrative safeguards (governance, risk analysis, training, incident response), physical safeguards (facility and device access controls), and technical safeguards (access controls, audit logs, encryption, and data integrity mechanisms).
How can AI systems create HIPAA compliance risks that traditional IT controls miss?
AI agents and LLM-based workflows can access, process, or surface ePHI in dynamic, unstructured ways that don't produce traditional audit logs. These gaps fall directly within the access control and audit control requirements of the HIPAA Security Rule , and closing them requires runtime governance tools built specifically for AI behavior, not legacy IT controls.